Installng SSL Certificates on Apache2 using OpenSSL
In this blog post, you can learn how to generate a CSR prior to acquiring your SSL certificates and how to later install them successfully on Apache2 web server.
Create a CSR
To activate an SSL certificate you need to submit a CSR (Certificate Signing Request) on our site. CSR is a block of code with encrypted information about your company and domain name.
Usually CSR openssl configuration contains by default the details as follows below:
It’s usually openssl that is used for CSR generation on Apache or Nginx web servers. It’s included by default in web servers’ properties. So if you have a web server installed, you will hardly need to install openssl additionally.
To generate a CSR run the command below in terminal:
We recommend you replace ‘server’ with the domain name the certificate will be issued for to avoid further confusion.
The command starts the process of CSR and Private Key generation. The Private Key will be required for certificate installation.
You will be prompted to fill in the information about your Company and domain name.
It is strongly recommended to fill all the required fields in. If a field is left blank, the CSR can be rejected during activation. For certificates with domain validation it is not mandatory to specify Organization and Organization Unit - you may fill the fields with ‘NA’ instead. In the Common Name field you need to enter the domain name the certificate should be issued for.
Please use only symbols of English alphanumeric alphabet. Otherwise the CSR can be rejected by a Certificate Authority.
If the certificate should be issued for a specific subdomain, you need to specify the subdomain in Common Name. For example ‘sub1.ssl-certificate-host.com’.
In case of Wildcard certificates, the domain name should start with an asterisk as in ‘*.ssl-certificate-host.com’
Once all the requested information is filled in, you should have *.csr and *.key files in the folder where the command has been run.
NOTE: To generate the CSR code with the Street address value included, add the 'Subject' ('-subj') tool with the corresponding data to the command as follows:
The command with the zip code included in the address should look the following way:
*.csr file contains the CSR code that you need to submit during certificate activation. It can be opened with a text editor. Usually it looks like a block of code with a header: “-----BEGIN CERTIFICATE REQUEST----“ It is recommended to submit a CSR with the header and footer.
*.key file is the Private Key, which will be used for decryption during SSL/TLS session establishment between a server and a client. It has such a header: “-----BEGIN RSA PRIVATE KEY-----“. Please make sure that the private key is saved as it will be impossible to install the certificate without it on the server afterwards.
- Common Name (the domain name certificate should be issued for)
- Country (two-letter code)
- State (or province)
- Locality (or city)
- Organization
- Organizational Unit (Department)
- E-mail address
It’s usually openssl that is used for CSR generation on Apache or Nginx web servers. It’s included by default in web servers’ properties. So if you have a web server installed, you will hardly need to install openssl additionally.
To generate a CSR run the command below in terminal:
openssl req -new -newkey rsa:2048 -nodes -keyout server.key -out server.csrWe recommend you replace ‘server’ with the domain name the certificate will be issued for to avoid further confusion.
The command starts the process of CSR and Private Key generation. The Private Key will be required for certificate installation.
You will be prompted to fill in the information about your Company and domain name.
It is strongly recommended to fill all the required fields in. If a field is left blank, the CSR can be rejected during activation. For certificates with domain validation it is not mandatory to specify Organization and Organization Unit - you may fill the fields with ‘NA’ instead. In the Common Name field you need to enter the domain name the certificate should be issued for.
Please use only symbols of English alphanumeric alphabet. Otherwise the CSR can be rejected by a Certificate Authority.
If the certificate should be issued for a specific subdomain, you need to specify the subdomain in Common Name. For example ‘sub1.ssl-certificate-host.com’.
In case of Wildcard certificates, the domain name should start with an asterisk as in ‘*.ssl-certificate-host.com’
Once all the requested information is filled in, you should have *.csr and *.key files in the folder where the command has been run.
NOTE: To generate the CSR code with the Street address value included, add the 'Subject' ('-subj') tool with the corresponding data to the command as follows:
openssl req -nodes -newkey rsa:2048 -keyout server.key -out server.csr -subj "/C=GB/ST=Yorks/L=York/O=My Company Ltd./OU=IT/CN=nctest.info/streetAddress=Example Avenue 1"The command with the zip code included in the address should look the following way:
openssl req -nodes -newkey rsa:2048 -keyout server.key -out server.csr -subj "/C=GB/ST=Yorks/L=York/O=My Company Ltd./OU=IT/CN=nctest.info/streetAddress=Example Avenue 1/postalCode=123456"*.csr file contains the CSR code that you need to submit during certificate activation. It can be opened with a text editor. Usually it looks like a block of code with a header: “-----BEGIN CERTIFICATE REQUEST----“ It is recommended to submit a CSR with the header and footer.
*.key file is the Private Key, which will be used for decryption during SSL/TLS session establishment between a server and a client. It has such a header: “-----BEGIN RSA PRIVATE KEY-----“. Please make sure that the private key is saved as it will be impossible to install the certificate without it on the server afterwards.
Installing an SSL certificate on Apache
Before you start the SSL installation process, please make sure that the CSR code is generated, all validation requirements are met, and the SSL certificate is issued and downloaded.
The next prerequisites are intended to ease SSL installation and help you avoid the common pitfalls:
As you may know, there are many Linux distributions where an Apache HTTP server can be installed. In this article, we will review SSL installation steps for two major operating system families: Debian-based and RHEL-based ones.
Debian, Ubuntu
For an Apache web server to run an encrypted HTTPS connection, make sure that the SSL mode is enabled by using this command:
Upload the SSL certificate files (.crt and .ca-bundle) to your server to the /etc/ssl/ folder and move the private key file (.key) to /etc/ssl/private/ for your convenience.
To start the SSL installation, locate the Apache configuration file which contains... settings for the HTTP connection of your website.
The default location of this file may vary and depends on the server configuration and the OS version.
In most cases, the appropriate configuration file (symbolic link) for the enabled HTTP website can be found in the /etc/apache2/sites-enabled/ directory for Debian and Ubuntu OS.
The following command may be helpful to find the proper configuration file:
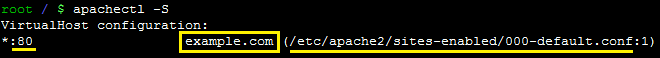
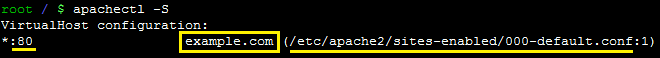
The output may display a port (80), domain name (example.com), the conf file path (/etc/apache2/sites-enabled/000-default.conf) and line number (1) where Virtual Host for the HTTP connection starts.
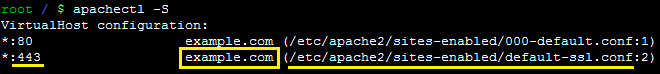
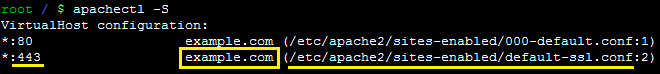
The next output indicates that Apache already has a configuration file for a secure HTTPS connection, so you need to update it according to the SSL renewal section.
If you do not see the configuration file for secure connection (*:443 line with your domain name), a new SSL installation is required. Follow these instructions:
Make a replica of the configuration file where Virtual Host settings for the HTTP connection is located. This command may be helpful:
Note! A new configuration file should be created in the sites-available directory.
Open the new configuration file with any text editor, change the port to 443 (default for the HTTPS connection) and add SSL directives. The example of a new Virtual Host for 443 may look like:
Note! Starting from Apache 2.4.8, the “SSLCertificateChainFile” directive became obsolete. Intermediate certificates (CA bundle) can be added to the “SSLCertificateFile” right after the certificate code.
Enable the new SSL configuration file by running this command:
When a new VirtualHost is created, save the file and run the syntax check:
If you are using virutal SSL enabled hosts be sure to add a default SSL Certificate to your Apache2 default-ssl.conf file. For example, the following lines should also appear in your Apache2 default-ssl.conf file:
If the system shows “Syntax OK”, reload the Apache for the changes to make effect with the following command:
Should any syntax error appears, it will be shown right away for troubleshooting.
The SSL installation can be verified using these tools:
https://decoder.link/sslchecker
https://www.ssllabs.com/ssltest/index.html
To save the SEO ranking, it is recommended redirecting all HTTP requests to the secure HTTPS version of your website permanently.
Note! If you are using a multi-domain or wildcard certificate, it is necessary to modify the configuration files for each domain/subdomain for which the SSL certificate is issued, unless this domain is used as ServerAlias. You would need to specify the domain/subdomain you need to secure and refer to the same certificate files in the VirtualHost record the way described above.
- Having access to the hosting server configuration over SSH via the terminal.
- The website should be working over the HTTP connection (default port 80)
- The private key should be located and matched with the SSL certificate. Check this article to find the private key and match it with the SSL certificate using this tool.
As you may know, there are many Linux distributions where an Apache HTTP server can be installed. In this article, we will review SSL installation steps for two major operating system families: Debian-based and RHEL-based ones.
Debian, Ubuntu
For an Apache web server to run an encrypted HTTPS connection, make sure that the SSL mode is enabled by using this command:
sudo a2enmod sslUpload the SSL certificate files (.crt and .ca-bundle) to your server to the /etc/ssl/ folder and move the private key file (.key) to /etc/ssl/private/ for your convenience.
To start the SSL installation, locate the Apache configuration file which contains
In most cases, the appropriate configuration file (symbolic link) for the enabled HTTP website can be found in the /etc/apache2/sites-enabled/ directory for Debian and Ubuntu OS.
The following command may be helpful to find the proper configuration file:
apachectl -SThe output may display a port (80), domain name (example.com), the conf file path (/etc/apache2/sites-enabled/000-default.conf) and line number (1) where Virtual Host for the HTTP connection starts.
The next output indicates that Apache already has a configuration file for a secure HTTPS connection, so you need to update it according to the SSL renewal section.
If you do not see the configuration file for secure connection (*:443 line with your domain name), a new SSL installation is required. Follow these instructions:
Make a replica of the configuration file where Virtual Host settings for the HTTP connection is located. This command may be helpful:
cp /etc/apache2/sites-available/your_website.conf /etc/apache2/sites-available/your_website-ssl.confNote! A new configuration file should be created in the sites-available directory.
Open the new configuration file with any text editor, change the port to 443 (default for the HTTPS connection) and add SSL directives. The example of a new Virtual Host for 443 may look like:
<VirtualHost *:443>
ServerName example.com
DocumentRoot /var/www/
SSLEngine on
SSLCertificateFile /etc/ssl/example_com.crt
SSLCertificateKeyFile /etc/ssl/private/example_com.key
SSLCertificateChainFile /etc/ssl/example_com.ca-bundle
DocumentRoot /var/www/example_com
ErrorLog /var/log/apache2/error.log
CustomLog /var/log/apache2/access_example_com.log "combined"
<Directory /var/www/html/example_com>
allow from all
Options None
Require all granted
</Directory>
</VirtualHost>
Note! Starting from Apache 2.4.8, the “SSLCertificateChainFile” directive became obsolete. Intermediate certificates (CA bundle) can be added to the “SSLCertificateFile” right after the certificate code.
Enable the new SSL configuration file by running this command:
sudo a2ensite your_website-ssl.confWhen a new VirtualHost is created, save the file and run the syntax check:
apachectl -tIf you are using virutal SSL enabled hosts be sure to add a default SSL Certificate to your Apache2 default-ssl.conf file. For example, the following lines should also appear in your Apache2 default-ssl.conf file:
SSLEngine on
SSLCertificateFile /etc/ssl/example_com.crt
SSLCertificateKeyFile /etc/ssl/private/example_com.key
SSLCertificateChainFile /etc/ssl/example_com.ca-bundle
If the system shows “Syntax OK”, reload the Apache for the changes to make effect with the following command:
sudo service apache2 reloadShould any syntax error appears, it will be shown right away for troubleshooting.
The SSL installation can be verified using these tools:
https://decoder.link/sslchecker
https://www.ssllabs.com/ssltest/index.html
To save the SEO ranking, it is recommended redirecting all HTTP requests to the secure HTTPS version of your website permanently.
Note! If you are using a multi-domain or wildcard certificate, it is necessary to modify the configuration files for each domain/subdomain for which the SSL certificate is issued, unless this domain is used as ServerAlias. You would need to specify the domain/subdomain you need to secure and refer to the same certificate files in the VirtualHost record the way described above.